If you do a default installation of the WebLogic Server user activity is not audited. WebLogic has a build in Auditing Provider but it has to be enabled.
The Audit Provider can log these events.
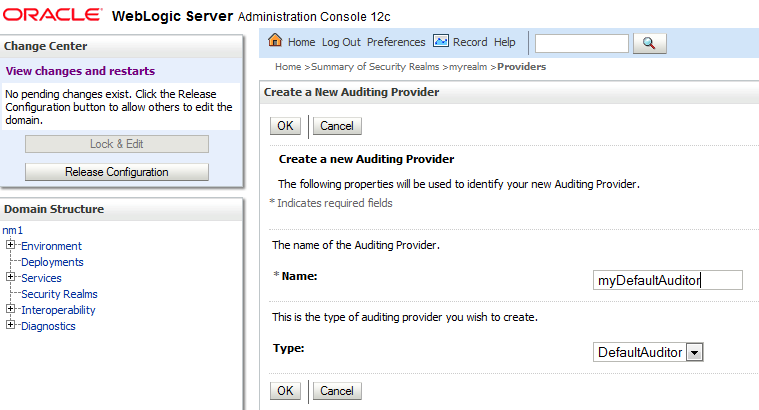
To enable it via the Admin Console got to Security Realms => myrealm => Providers => Auditing. Press New, select DefaultAuditor and fill in a Name:
Restart the Admin Server.
Now a DefaultAuditRecorder.log file will be created. For the Admin Server it will default be placed with the other logs in:
DOMAIN_HOME/servers/AdminServer/logs
If you log on to an application deployed to a Managed Server it will be placed in the logs directory for the Managed Server.
If you want the log files to be placed in a different location you can use this Java startup parameter:
-Dweblogic.security.audit.auditLogDir=/u01/app/oracle/logs
Try logging in to the Admin Console and check the log file. You will see something like this:
#### Audit Record Begin <Feb 9, 2013 11:16:12 AM> <Severity =SUCCESS>
<<<Event Type = Authentication Audit Event>
<lorenzen><AUTHENTICATE>>> Audit Record End ####
Principal = class weblogic.security.principal.WLSUserImpl("lorenzen")
Principal = class weblogic.security.principal.WLSUserImpl("lorenzen")
The logging event was AUTHENTICATE and the user lorenzen.
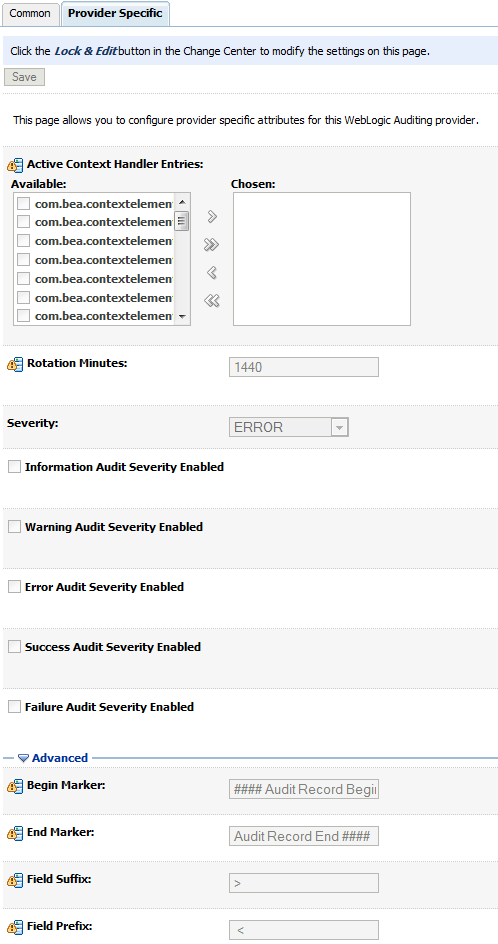
You can change miscellaneous setting for the Provider via the Admin Console:
- Log rotation interval
- The begin and end tag (Marker)
Configuration Auditing.
It is also possible to Audit configuration changes in the domain. It is up to you if you want the audit information to go to the WebLogic server log, to the Audit Provider or both. See how it is configure here.
Here is an example from the WebLogic server log where the number of log Files to retain is changed from 99 to 77:
####<Feb 9, 2013 12:52:35 PM CET> <Info> <Configuration Audit> <wintermute> <AdminServer><[ACTIVE] ExecuteThread: '3' for queue: 'weblogic.kernel.Default (self-tuning)'> <weblogic> <> <> <1360410755684> <BEA-159904> <USER weblogic MODIFIED com.bea:Name=nm1,Type=Log ATTRIBUTE FileCount FROM 99 TO 77>
 Twitter
Twitter LinkedIn
LinkedIn GitHub
GitHub GoodReads
GoodReads Last.fm
Last.fm
{ 1 comment… read it below or add one }
Very useful information. Thanks.